Scroll to explore
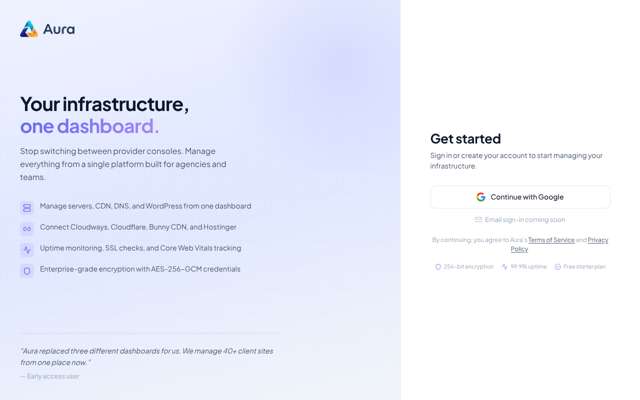
https://my-aura.app/
Roast Complete

“Aura addresses a genuine pain point for infrastructure managers, but the execution is currently blocked by a fragile, mandatory OAuth-only login flow. While the technical depth of the Digitizer Site Worker is impressive, the inability to access the dashboard makes it impossible to validate the 'unified' promise.”
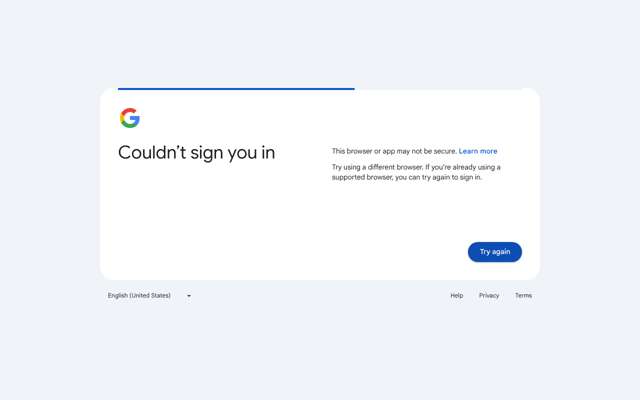
Biggest friction: Mandatory Google OAuth that fails with browser security errors, preventing any access to the product.
Best thing: The technical transparency and open-source nature of the Digitizer Site Worker plugin.
Confidence over time
Idea Assessment
A unified management dashboard for infrastructure providers like Cloudways, Cloudflare, and Bunny CDN, paired with an open-source WordPress management plugin.
I still don't know if the 'unified' dashboard actually simplifies workflows or just adds another layer of abstraction over existing APIs.
Landing Page
Clean, professional, and clearly targeted at technical users who are tired of console-hopping.
Missing: Interactive dashboard preview or video walkthrough • Standard email/password authentication • Clearer documentation on API integration limits
Journey — 7 steps

“The value proposition hits home—I'm tired of context-switching between provider consoles. The focus on API-driven management and security (AES-256-GCM) is promising, but I need to see if the 'unified' aspect actually reduces complexity or just adds another layer. I'm skeptical about the 'early access' gate, but the feature set looks relevant to my pain points.”

“This is exactly the kind of technical depth I look for. The fact that it's open-source and has a clear security model (IP whitelisting + tokens) makes me feel much better about connecting my infrastructure. It addresses my frustration with manual updates across multiple sites. I'm impressed by the 'zero frontend impact' claim—that's a critical requirement for my production environments.”
“The 'About' page confirms my suspicion that this is built by practitioners, not just marketers. The focus on 'Security First' and 'Open & Transparent' aligns with my need for technical depth. Seeing real companies like Deci and Reposify as users adds significant credibility. I have enough information to move to the signup phase to see if the dashboard lives up to the promise.”
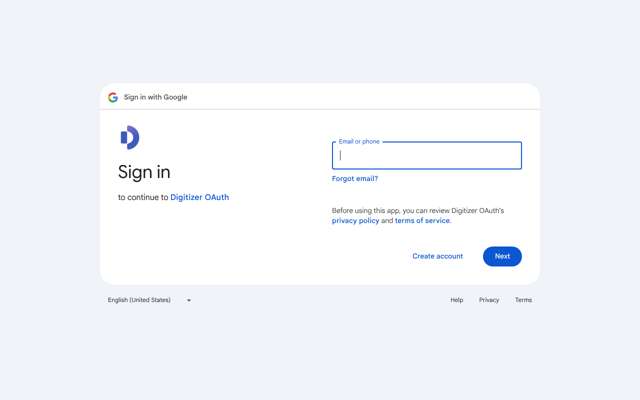
“I'm a bit annoyed that I can't use my work email directly, as I prefer to keep my professional tools separate from my personal Google account. However, the security mention of AES-256-GCM encryption for credentials on the previous pages gives me enough confidence to proceed with the OAuth flow to see the dashboard.”
“This is a standard OAuth flow. While I'm still slightly annoyed about the lack of native email/password login, I need to proceed to actually see the dashboard and evaluate the product's core value proposition.”
“Standard Google OAuth flow. I'm ready to move past this and finally see the actual dashboard to evaluate if the 'unified management' claim holds up or if it's just another layer of complexity.”
“This is incredibly frustrating. I've already expressed my annoyance at the lack of a native email/password login, and now the mandatory OAuth flow is failing entirely. It's a major barrier to entry for a product that claims to simplify infrastructure management. If I can't even get into the dashboard, I can't evaluate the actual value proposition.”
Diagnosis
The primary barrier to conversion is a broken and restrictive authentication flow that prevents users from accessing the platform. Because the login process relies exclusively on a failing OAuth implementation, potential users are unable to bypass the 'early access' wall to evaluate the product.
What costs you conversions
Deal Breakers
The OAuth authentication loop is failing to redirect users to the application, effectively preventing all new signups.
What Works
Action Plan
Implement a standard email/password authentication registration form
Only 'Sign in with Google' button present
Email input field, password input field, and 'Create Account' button added below the OAuth button
Users are currently blocked by the fragile OAuth flow; this provides a reliable fallback.
Fix server-side routing for 404 error pages
Broken routing causing improper status codes
Server returns a proper 404 HTTP status code for non-existent routes
Technical recommendation to improve site reliability and SEO indexing.
Add Open Graph meta tags to all primary pages
Missing social sharing metadata
Include og:title, og:description, and og:image tags in the <head> of the landing page
Increases professional credibility when links are shared by potential users.
Increase padding on all primary Call-to-Action buttons
Buttons are cramped and fail accessibility standards
Increase padding to 16px vertical and 32px horizontal
Ensures accessibility and improves usability for infrastructure managers on various devices.
Add a dedicated 'Compliance' section to the landing page footer
Compliance status is not explicitly stated in a clear, reassuring way
Add a 'Compliance' link in the footer that leads to a page detailing GDPR and SOC2 roadmap status
Arjun Müller noted the need for concrete data to reassure enterprise-level users.
Quick Wins
Growth Potential
Based on b2b_saas benchmarks (Unbounce, Portent, Google)
potential revenue
$45,000/mo
Based on MainWP ($4M ARR)
currently realized
47%
$21,150/mo
uplift
-8%
more conversions
The market for WordPress and infrastructure management is highly fragmented but has a high willingness to pay among agencies, allowing for a sustainable mid-market revenue stream through tiered subscription models.